TRUSTED BY THE WORLD'S LEADING ENTERPRISES
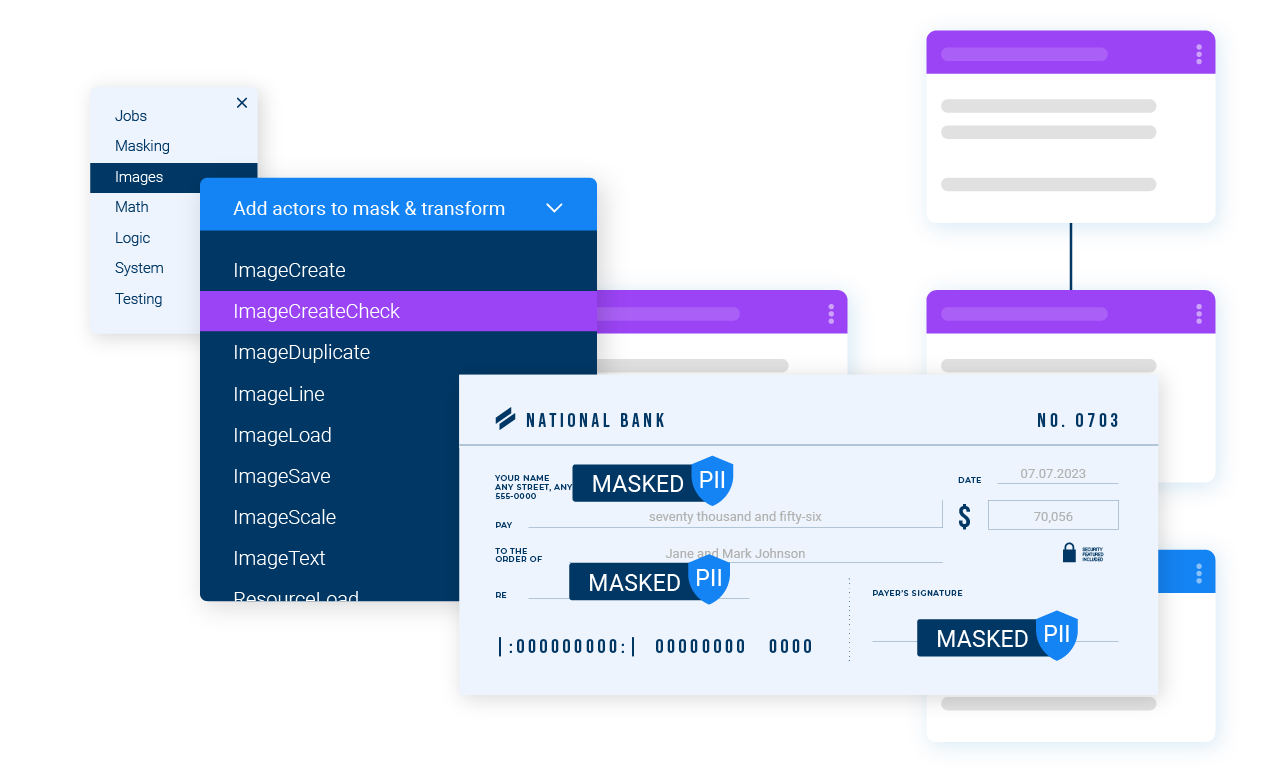
Mask any data, any way
Mask data in flight or at rest across complex enterprise data sources, structured and unstructured.
Simplify masking operations
Define masking rules once and apply them consistently, without dealing with systems, DBs, or schemas.
Preserve data integrity
Mask sensitive data consistently while keeping it accurate, usable, and compliant across systems.
Achieve data compliance for peace of mind
K2view mask data at the business-entity level, so sensitive data stays structurally accurate, compliant by default, and simple to manage across complex enterprise systems.

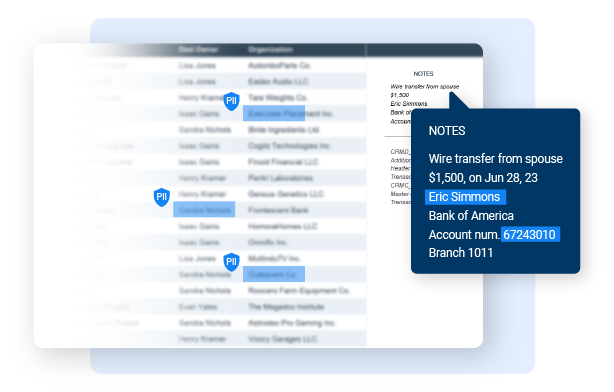
Unify data by business entity
K2view automatically discovers and unifies all sensitive data related to a business entity across tables, databases, and systems.
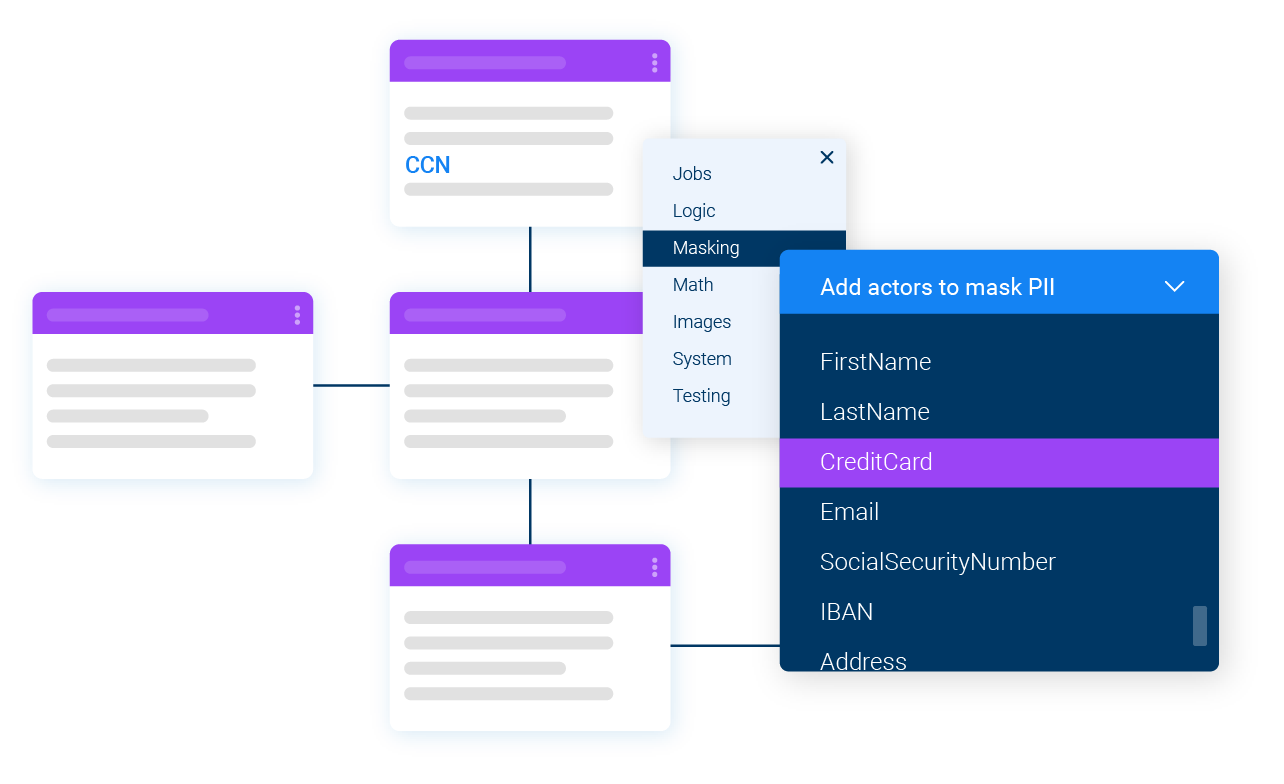
Mask once, apply everywhere
Masking rules are applied at the business-entity level and enforced consistently across all data sources and environments.
Deliver complete, reliable data
Auto-discover business entity schemas and auto-classify the PII and sensitive data for the business entities
K2view ingests multi-source data and automatically organizes it by business entities, in flight, to enforce referential integrity and contextual masking
Data is then masked in the context of the business entity and delivered to any target system or data store, with referential integrity preserved
Automate sensitive data governance
-
Automatically discover and classify sensitive data across systems by scanning both metadata and data content.
-
Define masking policies once in a centralized data catalog and enforce them consistently across all data sources.
-
Generate compliance-ready reports automatically to support audits and regulatory requirements.
Cover every data masking use case
-
Apply the right masking technique for each scenario, using built-in functions or custom logic
-
Provision compliant, production-like datasets for testing, analytics, B2B data sharing, and AI workloads using static data masking.
-
Enable controlled access to sensitive data, with reversible masking through pseudonymization and tokenization.
See our data masking tool in action
Take a product tour of key masking workflows, step by step.
Business outcomes powered by entity-based data masking
Deliver compliant test data on demand to keep testing fast and releases moving.
Accelerate software delivery
Mask data rapidly and reliably for compliant, up-to-date testing.
Ensure data compliance
Enforce consistent PII protection across all non-production environments.
Cut tooling and licensing costs
Consolidate data masking to reduce tooling sprawl, licensing, and overhead.
Secure B2B collaboration
Safely share compliant data with external partners, without exposing sensitive information.
INTERACTIVE PRODUCT TOUR
Data Masking
Close
Take the product tour
K2view Data Masking
Mask data from any source quickly and easily with K2view while maintaining referential integrity
EXPERIENCE OUR Synthetic Data Generation TOOL
Take the interactive product tour
More ways to provision compliant data at scale
Test Data Management
- Self-service portal for dev and test teams
- Cross-system data subsetting
- Subset, reserve, rollback, and age test data
- All data sources, from mainframes to SaaS apps
- AI test data provisioning from test cases
Synthetic Data Management
- AI-based generation for regression testing
- Rule-based generation for new functionality testing
- Entity-based cloning for load testing
- Subset, reserve, rollback, and age synthetic data
- Provision synthetic data into lower environments
Book a demo and see entity-based data
masking in action
Consistent, compliant masking from discovery
through delivery.